ONNX Model Security Scanner
Scan Before You Load
Protect your systems from malicious machine learning models. This security scanner analyzes ONNX models for embedded URLs, code execution patterns, suspicious file paths, and other potential threats before loading them into ONNX Runtime.
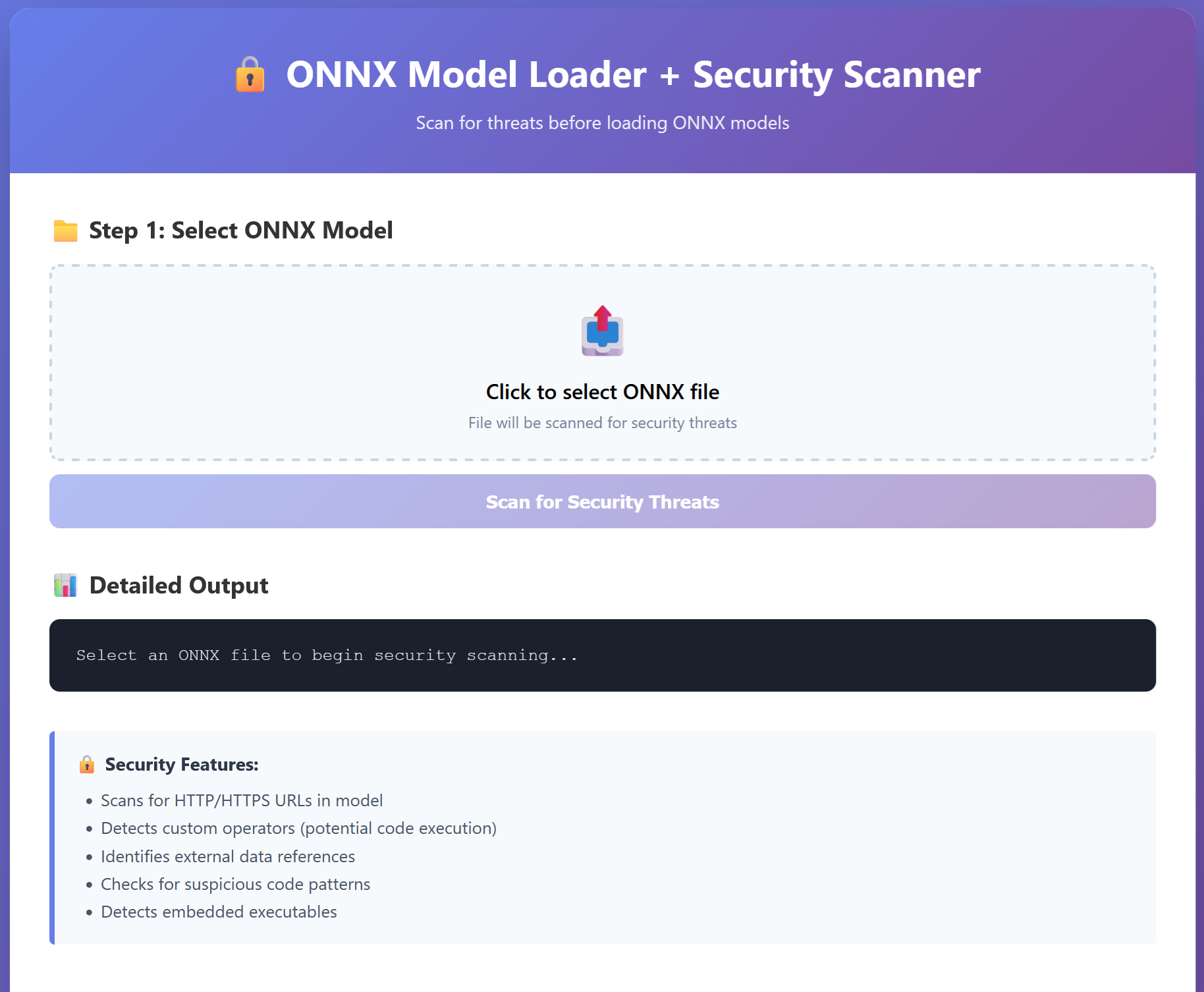
Security Features
URL Detection
Scans for embedded HTTP/HTTPS URLs that could be used for data exfiltration or command-and-control communication.
Custom Operator Detection
Identifies non-standard operator domains that may contain custom code execution capabilities.
External Data References
Detects references to external data files that could be used to load malicious payloads.
Code Execution Patterns
Searches for dangerous patterns like eval(), exec(), subprocess calls that indicate potential code execution.
Embedded Executables
Detects PE (Windows) and ELF (Linux) executable headers that may indicate embedded malware.
Network Operations
Identifies network-related strings like socket, connect, curl that could enable remote communication.
File Path Analysis
Detects suspicious file paths including path traversal attempts and system directory references.
Entropy Analysis
Calculates file entropy to detect encrypted or heavily obfuscated content that may hide malicious code.
Why Scan ONNX Models?
- Models from untrusted sources may contain malware
- Supply chain attacks target ML pipelines
- Custom operators can execute arbitrary code
- External data references can load payloads
- Embedded URLs enable C2 communication
- Protect production environments